Arthur Besse
cultural reviewer and dabbler in stylistic premonitions
- 27 Posts
- 87 Comments

 30·4 days ago
30·4 days ago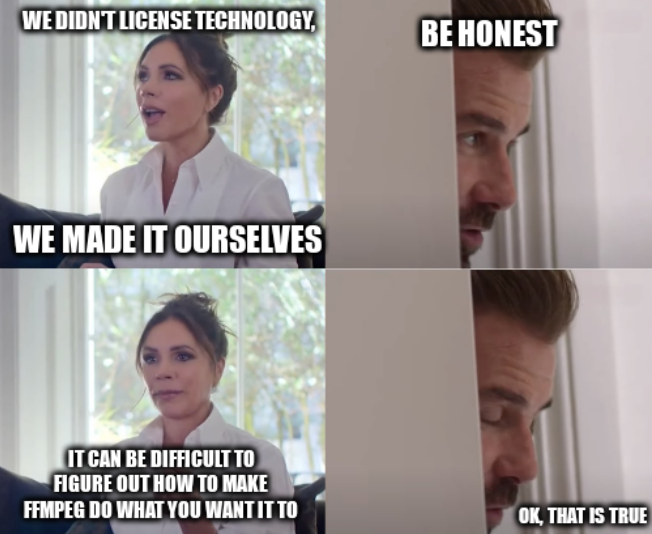

 6·7 days ago
6·7 days agoyou could use the clipboard to copy the link and open it in another browser
only hobbyists and artisans still use the standalone
carrot.pythat depends onpeeler.in enterprise environments everyone uses the
pymixedveggiespackage (created usingpip freezeof course) which helpfully vendors the latest peeled carrot along with many other things. just unpack it into a clean container and go on your way.
deleted by creator
deleted by creator
deleted by creator
does your resume include a sokoban clone?

 12·1 month ago
12·1 month agoThe headline should mention that they’re breaking 22-bit RSA, but then it would get a lot less clicks.
A different group of Chinese researchers set what I think is the current record when they factored a 48-bit number with a quantum computer two years ago: https://arxiv.org/abs/2212.12372
I guess the news here is that now they’ve reached 22 bits using the quantum annealing technique which works on D-Wave’s commercially-available quantum computers? That approach was previously able to factor an 18-bit number in 2018.
🥂 to the researchers, but 👎 to the clickbait headline writers. This is still nowhere near being a CRQC (cryptanalytically-relevant quantum computer).

 10·1 month ago
10·1 month agoAll two-letter TLDs are ccTLDs.
However, several of them are not in ISO 3166-1.

 4·2 months ago
4·2 months agoyep, the concept of a “personal carbon footprint” was literally invented by an advertising agency working for British Petroleum https://www.theguardian.com/commentisfree/2021/aug/23/big-oil-coined-carbon-footprints-to-blame-us-for-their-greed-keep-them-on-the-hook
Formally.

 21·2 months ago
21·2 months agoI really don’t get how its different than a search engine
Neither did this guy.
The difference is that LLM output is (in the formal sense) bullshit.

 16·3 months ago
16·3 months ago
 23·3 months ago
23·3 months agoUpload bandwidth doesn’t magically turn into download bandwidth
Actually, it does. Various Cable and DSL standards involve splitting up a big (eg, measured in MHz) band of the spectrum into many small (eg, around 4 or 8 kHz wide) channels which are each used unidirectionally. By allocating more of these channels to one direction, it is possible to (literally) devote more band width - both the kinds measured in kilohertz and megabits - to one of the directions than is possible in a symmetric configuration.
Of course, since the combined up and down maximum throughput configured to be allowed for most plans is nowhere near the limit of what is physically available, the cynical answer that it is actually just capitalism doing value-based pricing to maximize revenue is also a correct explanation.

 4·3 months ago
4·3 months ago
ip -br a(
-bris short for-briefand makesip’saddr,link, andneighcommands “Print only basic information in a tabular format for better readability.”)

 6·4 months ago
6·4 months agoadding all compiled file types including .pyc to .gitignore would fix it
But in this case they didn’t accidentally put the token in git; the place where they forgot to put
*.pycwas.dockerignore.

 9·4 months ago
9·4 months agoAt my workplace, we use the string @nocommit to designate code that shouldn’t be checked in
That approach seems useful but it wouldn’t have prevented the PyPI incident OP links to: the access token was temporarily entered in a
.pypython source file, but it was not committed to git. The leak was via.pyccompiled python files which made it into a published docker build.

 118·5 months ago
118·5 months agothis isn’t remotely how this meme is used lol

python -c 'print((61966753*385408813*916167677<<2).to_bytes(11).decode())'how?
$ python >>> b"Hello World".hex() '48656c6c6f20576f726c64' >>> 0x48656c6c6f20576f726c64 87521618088882533792115812 $ factor 87521618088882533792115812 87521618088882533792115812: 2 2 61966753 385408813 916167677